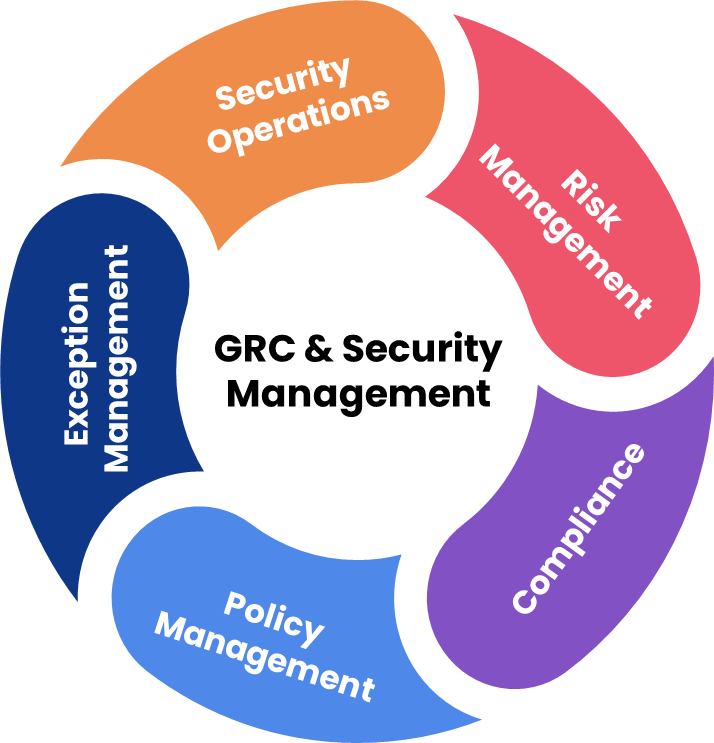
Our Unified Approach to Risk, Compliance, and Security Management for Enhanced Protection and Operational Efficiency
Your organization is under a constant onslaught of cyberattacks, vulnerabilities, malware, viruses, and many new threats every day. Additionally, you have to show how your systems and organization address data security, governance, risk, and compliance needs. And that’s on top of the constant stream of security updates for your software and systems.
How can you address this ever-expanding landscape of threats all while keeping headcount down and resources flat?
The key is taking a unified approach to risk, compliance, and security management, with the right combination of the three areas supporting your security needs: IT Service Management (ITSM); IT Governance, Risk, and Compliance Management (GRC); and Security Incident and Event Management (SIEM).
- T4S has a comprehensive approach to improving security management across any one or all three of these areas. We can help you by:
- Setting up the right processes for Governance, Risk, and Compliance (GRC) management using proven tools like Ivanti Neurons for GRC.
- We connect IT Asset Management tools and CMDB with your SIEM tools to give you complete visibility into the security status of all your systems and devices
- Helping you establish and execute a clear roadmap to building out the risk & security management capabilities of your IT organization.
Key Information Security Management Capabilities
T4S Partners can help you accelerate your Information Security program, minimize business risk, and strengthen your organization’s security posture.
Qualify Risk
Leverage reoccurring Audits and Risk Assessment to identify and quantify risk in a repeatable manner enabling you to track the impact of controls and risk remediations.
Collaborations
Support collaborations between multiple stakeholders, enabling effective information sharing, dialogue, and decision making.
Reduce Administration
Reduce or eliminate administrative use of tools like Excel for managing audit schedules, timelines, and closure of tickets. Avoid duplication of GRC-related tasks and disconnected results.
Real-Time Reporting
Provide evidence-based, real-time reports to executives and stakeholders and documented Risk acceptance sign-off assurance (instead of relying on verbal and undocumented sign-off.)